
In some testing sectors, it is routine to steal an entire test file including all item text, other resources (e.g., graphics, video, audio, etc.) and answers. The theft occurs before or after a scheduled exam administration after the files have been downloaded to a testing center’s server. The thieves penetrate IT security procedures through weak user access policies and procedures, and by decrypting (if the files are encrypted) the stolen files.
The theft of test files is a most dangerous type of theft because it provides the exact content of the questions and the answers. Once the method of theft is established, stealing any test file is routine, with virtually no risk of detection. The theft of test booklets provide the exact items, informing exact, but improper test preparation activities.
For paper‐and‐pencil tests, test booklets are shipped to testing locations and stored locally, perhaps in a locked file cabinet or room. Individuals may remove the booklets from the shipping container prior to storage, or may have access to the locked cabinet or room. Booklets may be stolen after test administration as booklets are returned to the storage are and prepared for return shipping the stolen files.
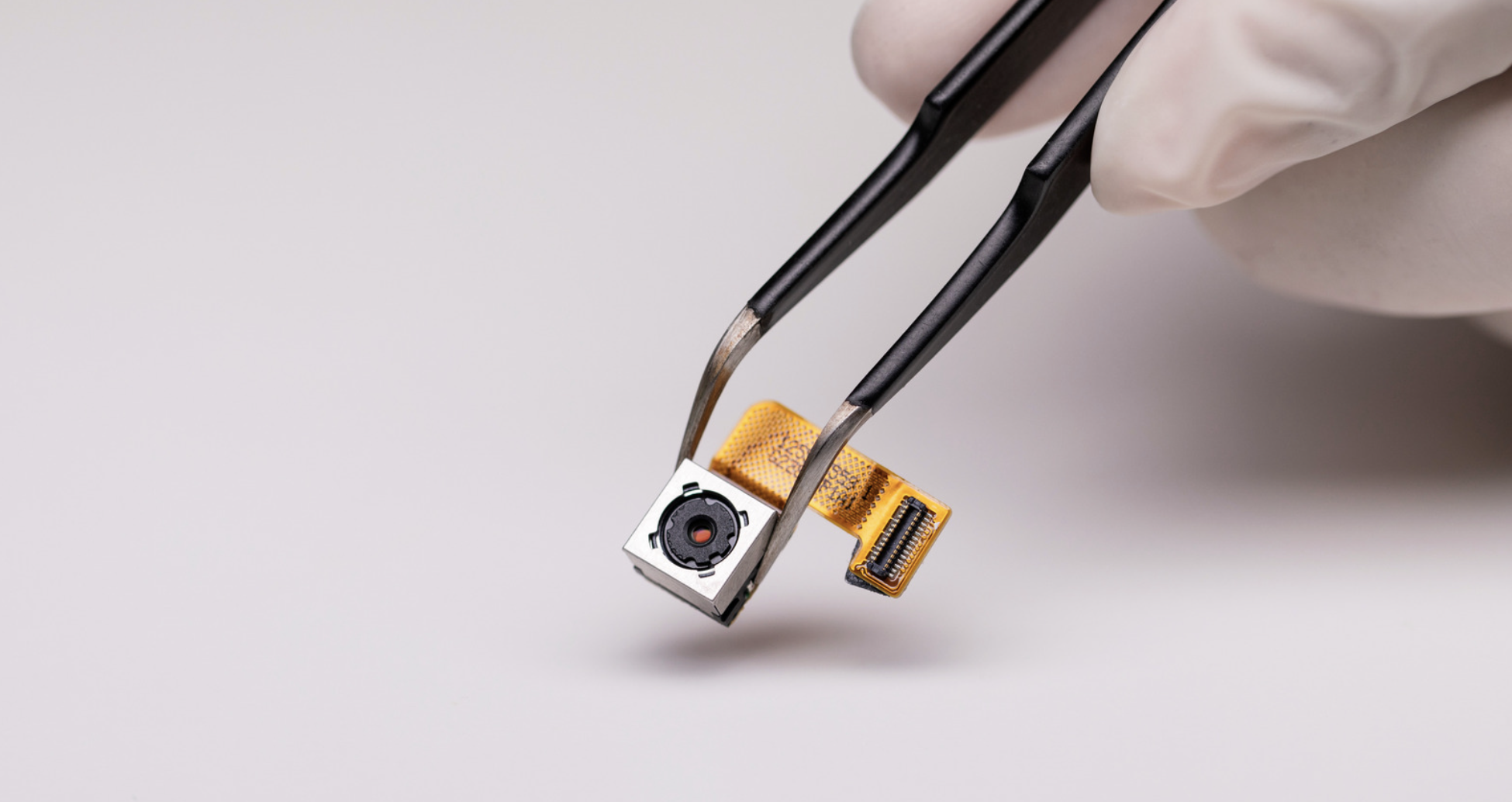
Test questions can be captured as they are displayed during a test, whether on a screen or a booklet. The thief may use a high‐resolution digital camera, cell phone camera, or one of the high‐quality so‐called “spy” cameras (hidden in glasses, pens, watches, etc.). These cameras are able to store video of and then transmit the content of exams.
This is a relatively manual capture of questions, which is easy to do and accurate. The hidden nature of the devices make detection by proctors very difficult, if not impossible. No answer key is captured.
This could happen simply by using Copy and Paste commands, or, with more difficulty, the entire test session, including all test questions, can be captured with a single automated procedure by using a TIVO‐like recording system connected to one of the computer’s output ports.
The Copy/Paste method is effective if no restrictions are placed on the testing system. The TIVO‐like method requires technical skills, especially as the items are recorded, stored, and transferred to other media (such as a document). No answer key is captured. The probability of detection by proctors is low once the equipment is in place.
Test takers memorize questions to be recalled at a later time. If part of an organized effort each may be “assigned” a particular subset of the question content. Mark‐and‐Review features of testing systems allow the thieves to “gather” their assigned items and concentrate their efforts.
The method needs no technology, but is difficult to do for tests designed to prevent or control item exposure. It also results in inaccuracies in the item content. No answer key is captured. Probability of detection is low.
Thieves use oral or written recordings of test item content during the exam. This may involve audio recording devices, text recording devices such as cell phones, or notepads/scratch paper. Thieves can also use two‐way radios or cell phones to capture and transmit the content of the questions.
This type of theft could take many forms. A test taker violates retake rules so that the test can be taken many times to make sure that all of the items can be completely harvested. A testing center may schedule an exam for a “phantom” test taker in order to access the files downloaded to its servers.
A testing center can control when and how they are able to capture test content, being able to meet their specific market needs.
An employee or contractor of a testing program, with access to some or all of the items, provides the items to confederates, usually for gain (e.g., money, revenge, etc).
The content will be accurate and damaging to a program. This type of fraud is rare and the risk of detection and criminal punishment is high.
Test taker obtains a copy of test questions and answers prior to the exam. These may be obtained from websites selling the exact questions, or from forums and chat sessions where some or many of the exams are discussed. This method of cheating depends on successful prior harvesting of the test content
The content is highly accurate and easily obtained. Actual cheating is very difficult to detect, and impossible to detect by test administrators and proctors.
With the help of the testing center personnel, experts in the tested content assist the test taker during the exam. These helpers may be actual teachers, instructors, or simply knowledgeable individuals. In some cases it may involve communication with the test taker via technologies such as cell phones or two‐way radios.
This type of cheating is not easily detected and reported because it often involves collusion with testing center personnel. High scores are assured.
Test takers use aids during the exam, such as cheat‐sheets, cell phones, headphones, programmable calculators, etc. Test takers may be able to access the Internet and its resources during the exam. These devices and resources contain test questions/answers or simply useful information about the subject matter being tested.
Test taker is able to access resources to cheat during the test. The use of these resources is very effective and they are designed to be difficult to detect. The resources may be helpful but not very accurate. A high score may not be assured.
It isn’t difficult to find a company or person offering proxy testing services to take the test for you. The services may even be located in another country. There is no need to attend the test session at all. These services often guarantee a high or passing score.
This method of cheating has the assurance of a high score, but it is expensive. Professional proxy test taking is difficult to detect as it involves collusion of testing center personnel.
For a smaller price, or even as a favor, a friend or acquaintance may take the test on behalf of the cheater.
This type of cheating is difficult to detect and is able to take advantage of weak authentication procedures. There is no assurance of a high score.
Exploiting weak user access systems, hackers can gain unauthorized access to a program’s test results database or scoring system. Once in the system they are able to change lower scores to higher ones, or simply delete the records.
This method of cheating takes many forms. Low‐performing students may be required to stay home on testing days. Test administrators may ask students to mark answers in a test booklet, which can be verified or changed by a proctor, before transferring them to answer sheets. Item timing rules can be overlooked allowing students more time. Overall average scores can be raised by removing the possibility of low scores or by changing low scores to high scores. Probability of detection is high.
It is difficult to change test administration procedures without risk of detection. Test takers and other test administrators may be alerted to the changes, particularly when procedures are clearly stated and have been established for years.
Even for a computerized test, it is possible to copy answers from a nearby test taker. Questions may not utilize randomization features making this method of cheating more effective.
This type of cheating carries a low risk and is mostly ineffective today with technology‐based tests because most current computerized tests are designed such that test takers do not see the same questions nor are they in the same order.




