
Five primary sources of data help us measure the effects of test security weaknesses, threats and vulnerabilities. This article focuses on one: data gathered from exam administrations.
In 1973, while discussing the computational difficulties of detecting answer copying on exams, William H. Angoff wrote:
“However, even a brief consideration of this solution [i.e., constructing theoretical statistical distributions of identical responses between random test takers] makes it clear that the complexities … are far too great to make it practical.”
A lot has happened in 40 years. The power and capacity of today’s computers have made “impractical” solutions possible. In this era of big data, smart people using computers are replacing yesterday’s imagining with today’s reality (e.g., digitization of human knowledge found in libraries, sequencing the human genome, etc.).
By applying computational models to databases containing observations and measurements, we can answer critical questions, such as how to improve test security. The statistician Edward W. Deming, who achieved fame by helping the Japanese industry achieve superb quality after World War II, stressed the importance of using data to improve systems and quality. Deming characterized the improvement process using the PDSA (plan, do, study, act) cycle. Every part of this cycle requires being able to measure outcomes and make positive change. Thus, analysis of data is vital for strengthening test security and ensuring that test scores have their intended meaning.
The five primary sources of data which help us measure the effects of test security weaknesses, threats and vulnerabilities include:
Data gathered from exam administrations (e.g., data forensics)
Tips received from concerned individuals (e.g., tip lines)
Information retrieved from searching the internet (e.g., web monitoring)
Reports written by proctors and invigilators (e.g., incident reports)
Observations where tests are administered (e.g., site monitoring and inspection)
Because Exam Administration is the point of attack for most thieves and cheaters, it is absolutely critical that test result data are analyzed to detect potential test security violations.
Credentialing programs should use and cultivate every source of data possible for improving test security. The remainder of this article focuses on the first source of data.
Test result data gathered during test administration arguably provide the richest source for learning about test security threats and weaknesses because test security threats are most prevalent during exam administration. More non-trusted individuals (some of whom are eager to steal and cheat) are exposed to the questions during exam administration than at any other time. During exam administration, cheaters seek to exploit every weakness and vulnerability in security procedures. Because exam administration is the point of attack for most thieves and cheaters, it is absolutely critical that test result data are analyzed to detect potential test security violations. A proper study of these data is necessary to improve test security using Deming’s PDSA improvement cycle.
While emphasizing that data must be studied, it would be shortsighted to not recognize that some data provide more information about test security threats (e.g., theft and cheating). Test theft can be accomplished using tiny cameras that record the testing session with no human interaction. Thus, there may be no evidence that the test taker did anything wrong. While detection of theft is difficult, certain types of cheating can be found easily using test result data.
Most cheating techniques fall into two categories: collusion between test takers and pre-knowledge
of disclosed exam questions. Collusion occurs when examinees share answers during the testing session (e.g., using cellphones) or breaks (e.g., in restrooms), or when surrogate test takers (i.e., proxies)
are employed. It can also happen when teachers or proctors coach test takers during the exam. A variation of collusion called tampering occurs when an exam administrator changes answers for test takers during or after the testing session. Pre-knowledge of exam content generally occurs through disclosure of secure test questions on the internet by an instructor or by rogue review courses.

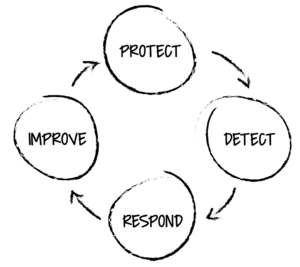
Figure 1: Four Key Phases of Continued Test Security Process



